NOTE: Really, guys of Security By Default blog published us (my good friend Roi Mallo and me) two articlesabout how to develop modules for Metasploit framework, another two are coming. ;)
During my project, among others, I developed a Metasploit module which can flood SIP protocol with common frames (INVITE, OPTIONS, REGISTER, BYE), I wrote it at Quobis (nice job ;) in order to use it for some private tests because actual software didn´t fit our needs, so we are going to probe how is the behavior of different GPL VoIP servers against this kind of attacks:
- Asterisk: I think it needs no introduction, the famous softswitch/PBX software.
- Freeswitch: It´s a newer softswitch that seems to be Asterisk replacement and I really like.
- Kamailio (former OpenSER): It is the most known GPL SIP proxy.
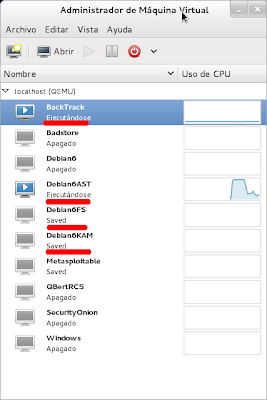
Virtual machines
First of all I want to be clear about two things:- Test were made without any protection on the server side, in a real environment we shoud find (in theory xD) something like Iptables, Snort, Fail2ban, Pike or a propietary Session border controller in large arquitectures. Anyway, it should be enough for this proof of concept.
- Asterisk and Freeswitch are PBX software, they were not designed to run between the limits of the infrastructure and Internet, although they are usually placed there. In fact, one of the reason of this post is to show the importance of using a SIP Proxy because of security and performance reasons.
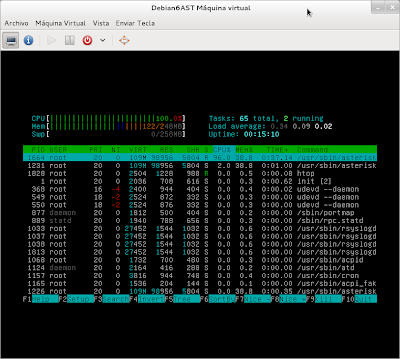
Next pictures show an example of the Metasploit module use and generated traffic, we will use the same attack against differents IPs, so I´m showing it once only:
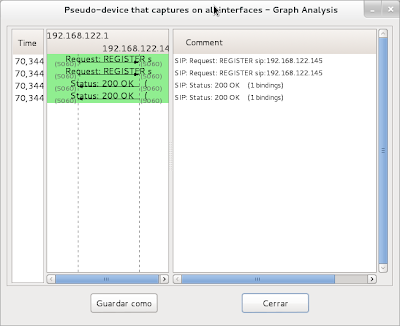
Captured traffic
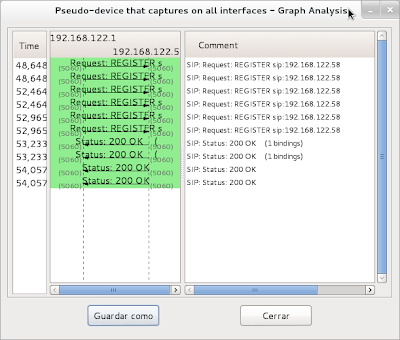
I chose INVITE packets because they are much more effective against all kind of SIP devices and TIMEOUT to 0 trying to get more traffic. Then, the results:NOTE: With Wireshark filter "sip.Method==REGISTER or sip.Status-Code==200 and !sdp" we can see if a softphone (Jitsi in this case) could be registered , this way we can confirm if tested software losts some REGISTER packages under attack.
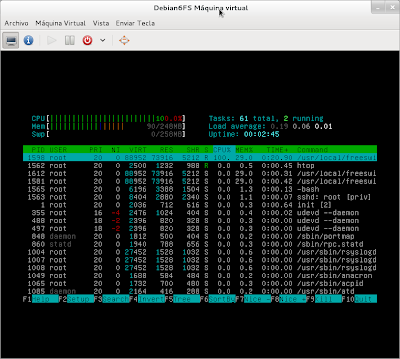
Metasploit vs. Asterisk
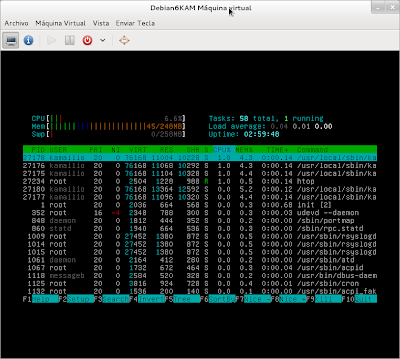
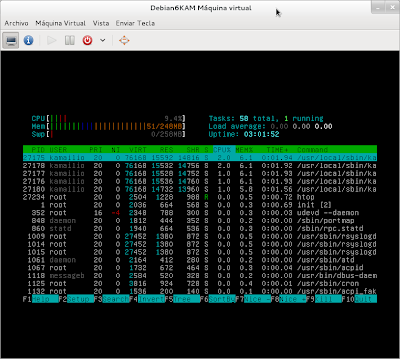
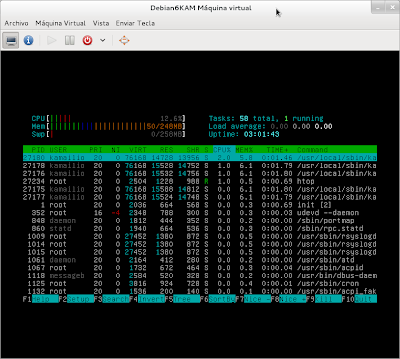
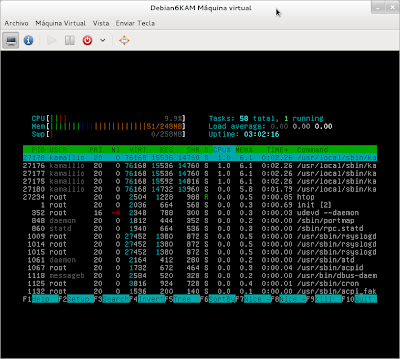
Metasploit vs. Kamailio
Pictures show how Metasploit module can flood both Asterisk and Freeswitch, but not Kamailio. Moreover, Asterisk lost REGISTER packets under the attack and Freeswitch did "strange" things answering with a lot of "200 OK" responses. This problem would be much more important in a real environment with hundreds of phones trying to register at the same time.
As conclusion we can confirm the use of Kamailio (I think OpenSIPS or another SIP Proxy would reach the same results) as frontier with "the wild". In addition we can also use Pike module for DoS protection and we could suppose that it would respond to a high volume of traffic in a better way than other two alternatives. To sum up I would like to remark that we can see Kamailio creates different forks to manage connections, this seems to be the key of its good performance. But next times I will show how to flood Kamailio with better results and the countermeasurements to protect yourself against it. ;)
As conclusion we can confirm the use of Kamailio (I think OpenSIPS or another SIP Proxy would reach the same results) as frontier with "the wild". In addition we can also use Pike module for DoS protection and we could suppose that it would respond to a high volume of traffic in a better way than other two alternatives. To sum up I would like to remark that we can see Kamailio creates different forks to manage connections, this seems to be the key of its good performance. But next times I will show how to flood Kamailio with better results and the countermeasurements to protect yourself against it. ;)