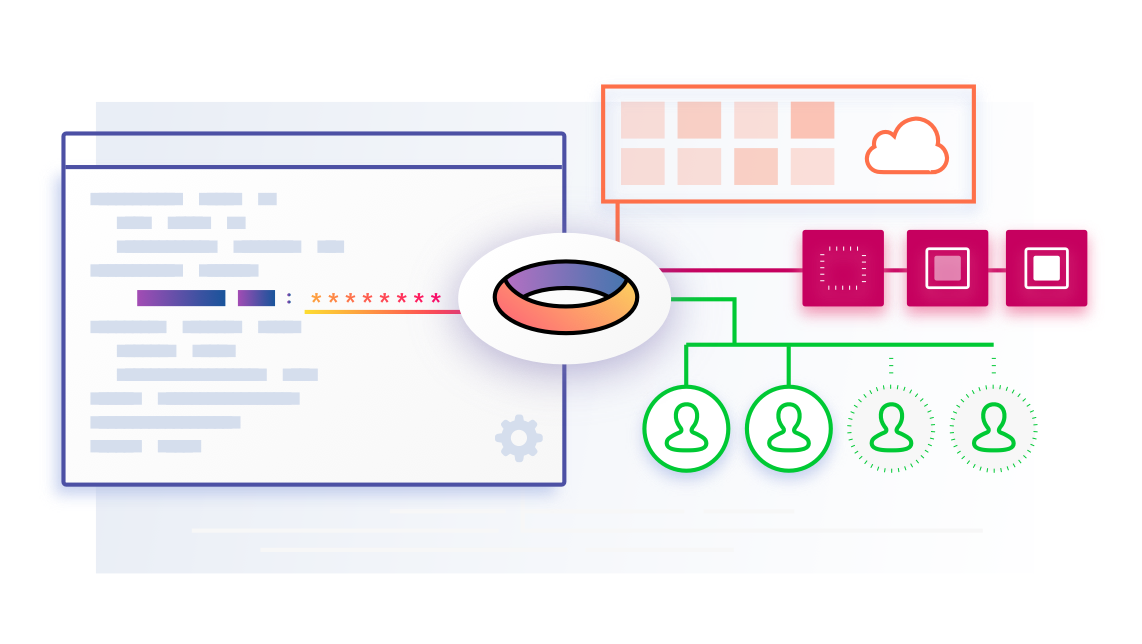
Development today relies on multiple teams, services, and environments all working in unison, and they’re difficult to orchestrate.
Mismanagement of secrets can land you on the front page of popular tech publications as part of an embarrassing data breach that results in loss of trust and future business. It happens to even the biggest of companies, for example: LinkedIn, Dropbox, Yahoo.
There is an ongoing tug of war between productivity and security which typically tips in favour of productivity. We take shortcuts and make mistakes resulting in compromised security posture.
You shouldn’t have to choose, so we’ve created Torus.
Allow me to demonstrate how easy it is to take a project (in this case, a readily available open source one) and configure it with Torus:
Choose your project
I need an application to start with, something that requires secrets.
I’ve chosen SlackIn, which is a utility that provides self-service sign-up for Slack teams. First we clone the repository:
$ git clone git@github.com:rauchg/slackin.git
$ cd slackin
Install the required dependencies:
$ npm installAnd if you haven’t already, install Torus and signup:
$ npm install -g torus-cli
$ torus signup
Link it up
We want to link our Torus account to the project using torus linkThis allows the codebase to be physically linked to the Torus project.
$ torus link
✔ Select organization: skywalker
✔ Create a new project: slackin
Project slackin created.
This directory and its subdirectories have been linked to:
Org: skywalker
Project: slackin
Use ‘torus status’ to view your full working context.
I now have a .torus.json file in the project directory. I’ll commit that to git:
$ git add .torus.json && git commit -m “Add .torus.json”By committing the .torus.json file, people who collaborate with me on this project will automatically be linked to the skywalker org and the slackinproject.
Secrets and where to store them
SlackIn accepts four different environment variables as config:
- SLACK_SUBDOMAIN
- SLACK_API_TOKEN
- SLACK_CHANNELS (optional)
- SLACK_COC (optional)
- PORT
We need to generate the two required SLACK items before going any further. We’re still in development, so let’s register a Slack team specifically for test purposes, and once we’re logged in as admin we’ll generate a new API token.
For demonstration purposes my development team name and token will be:
SLACK_SUBDOMAIN=skywalker-ranch-dev
SLACK_API_TOKEN=xoxp-8675309–9035768–1042534-r2d2
Now that I have these values in plain text (taken from the Slack website output), I need to store them for use in my application.
Inside every org each member is given their own development environment. This allows me to experiment, and develop without impacting secrets shared across multiple teams or services.
First I set the port that I want the process to listen on, in development:
$ torus set port 1337I set the subdomain and token value using torus set:
$ torus set slack_subdomain skywalker-ranch-dev
…
Credential slack_subdomain has been set at /skywalker/slackin/dev-jeff/default/*/*/slack_subdomain
$ torus set slack_api_token xoxp-8675309–9035768–1042534-r2d2
…
Credential slack_subdomain has been set at /skywalker/slackin/dev-jeff/default/*/*/slack_api_token
I’ll throw away the plaintext values, because I’ve now encrypted them inside Torus.
If I need to view the plaintext values, I can retrieve and decrypt the values using torus view.
$ torus view
SLACK_SUBDOMAIN=skywalker-ranch-dev
SLACK_API_TOKEN=xoxp-8675309–9035768–1042534-r2d2
PORT=1337